EncryptRIGHT®
EncryptRIGHT®
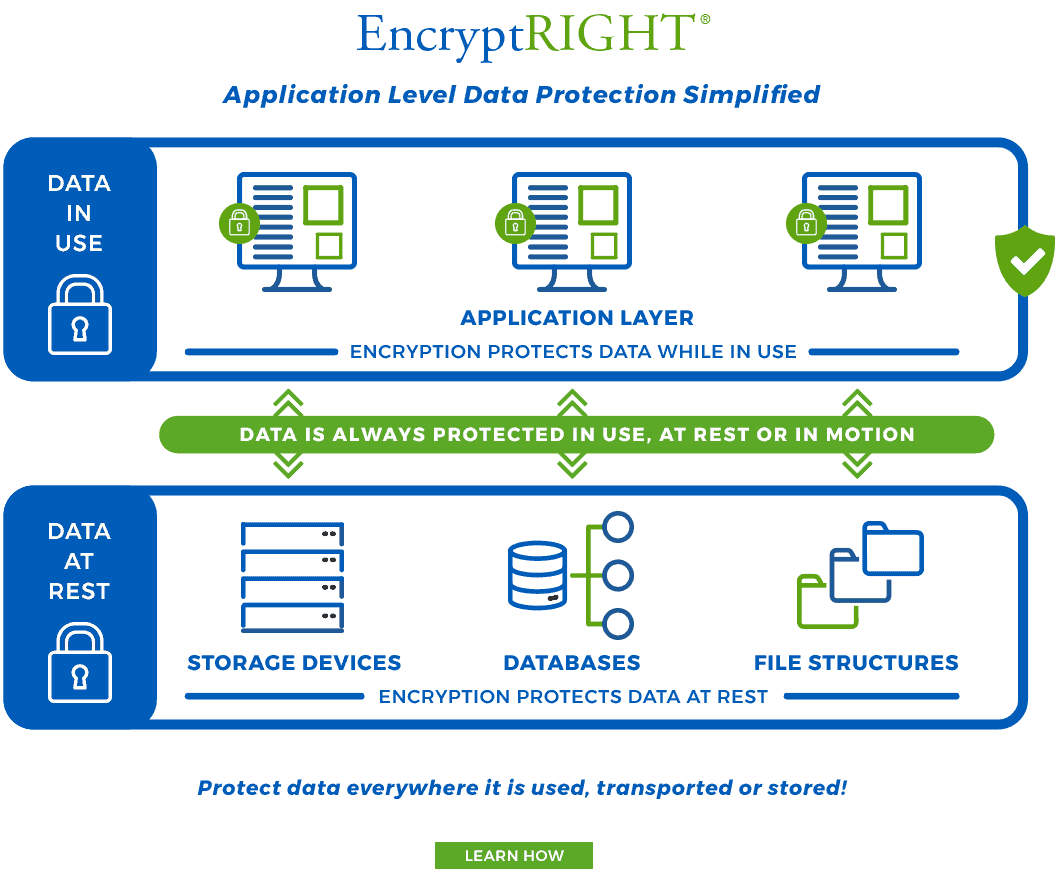
Application Level Data Protection Simplified
Traditional data protection solutions that protect sensitive data at the disk, database, or file structure level typically leave data exposed in the clear at the application level – the place where most successful data breaches occur. This gap in protecting sensitive information has been difficult to address because application level data protection is messy, complex, and impractical – until now.
EncryptRIGHT provides data encryption, tokenization, data masking, key management, audit-logging, and reporting functionality to protect Personally Identifiable Information (PII) and other sensitive data of global customers across many industries, including financial services, healthcare, global logistics, manufacturing, energy, and more. Whether complying with global data protection regulations or industry standards, reducing the scope of PCI-DSS audits, protecting privacy, pseudonymizing or anonymizing data, managing data sovereignty, or subpoena-proofing the cloud, EncryptRIGHT delivers a seamless data protection solution where data is most at risk of being breached.
EncryptRIGHT Features & Capabilities:
- Speed of Integration – Application-native data protection in as little as 3 lines of code
- Encryption – Application-level encryption, file encryption and Transparent Database Encryption (TDE)
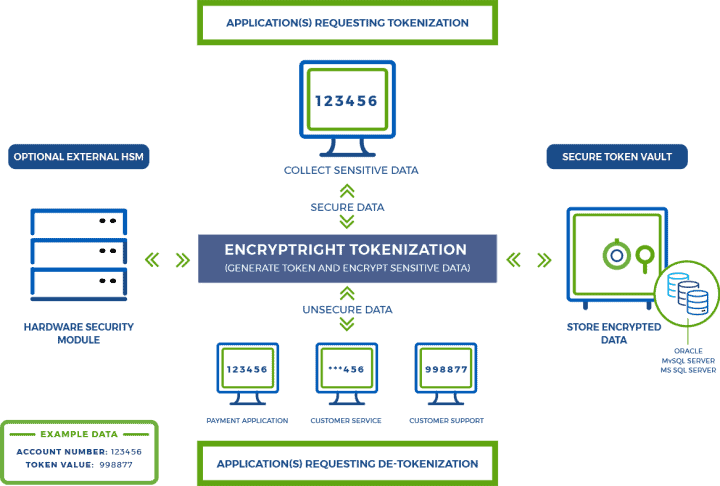
- Tokenization – Random-number generation or encryption generated, single- or multi-use tokens
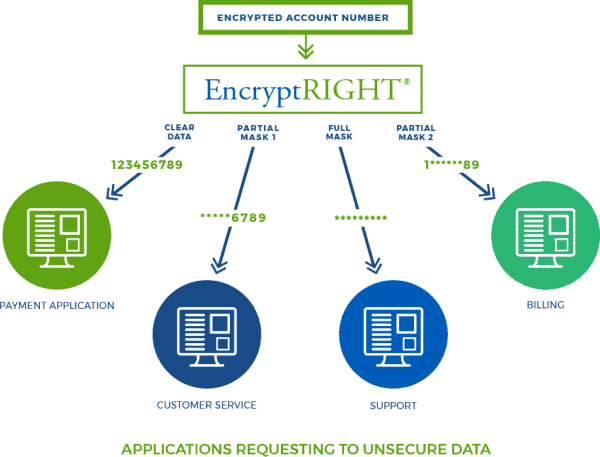
- Data Masking – Static or dynamic data masks applied based on predefined user permissions
- Role-Based Access Controls – Define users’ level of access to data – full, partial, or no access
- Data-Centric Security Architecture – Data Protection Policies (DPP)s that bind to the data itself
- Broad Compatibility – Out-of-the-box functionality for every common enterprise operating system
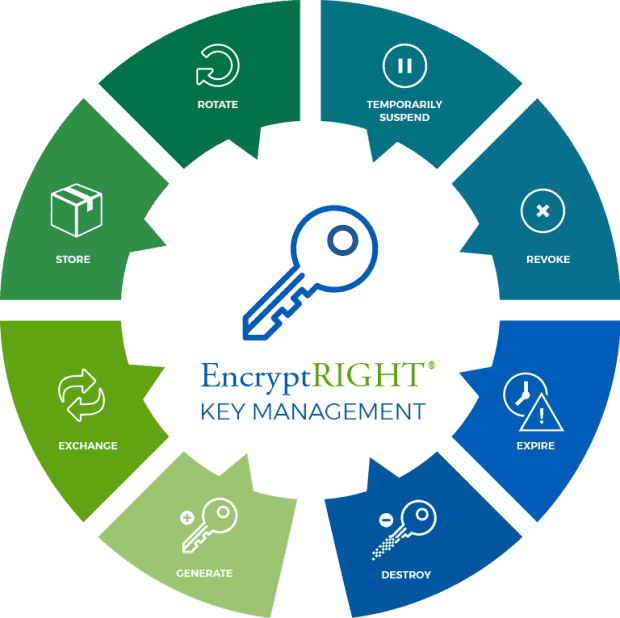
- Centralized Key Management – Key generation, rotation, exchange, revocation, and expiration
- Audit Logging & Alerts – Reports and audit trails for assessment and verification processes
- Deployment Flexibility – Deploys on premise, in private or public cloud, or in hybrid environments